Since version 9.40, Syncovery supports a safer way to store your passwords.
You have the choice between different safety levels:
- Legacy Encryption (Weak)
- Automatic Key Tied to This Computer (Medium Safe)
- Automatic Key Tied to This Windows User (Medium Safe)
- Password Phrase (High Safety if a good password is chosen)
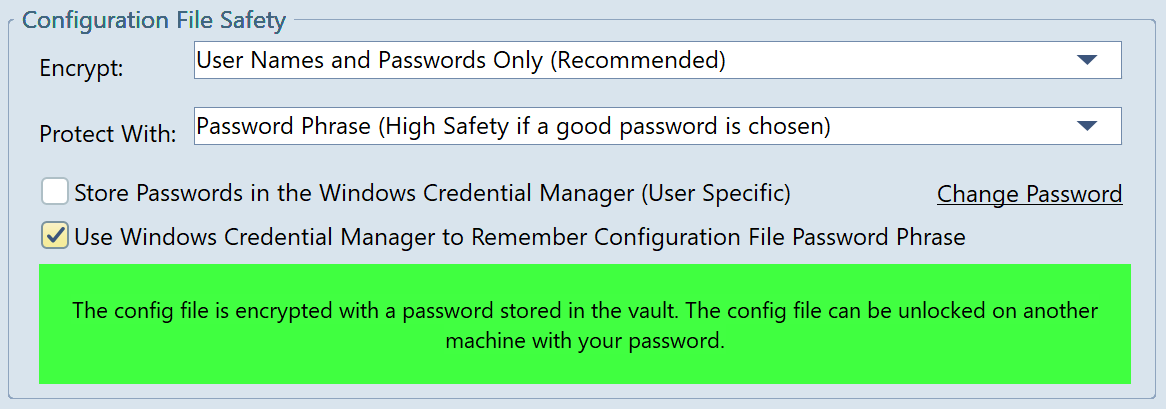
The safest encryption would require you to enter your encryption password every time you open Syncovery or start the scheduler. This is probably not feasible for servers, but you can also choose to store the settings encryption password in the Windows Credential Manager. Then it would work on servers, even after a reboot and if the scheduler runs as a service.
For medium safety (which should be good enough for many use cases), you can let Syncovery automatically generate an encryption key tied to your computer, or tied to to your user account on that computer.
These encryption methods also work when the scheduler runs as a service, and even if it runs under a different account. The service will communicate with the Syncovery GUI so that it gets access to the information needed to generate the encryption keys.
You can also choose to store passwords in the Windows Credential Manager (or just the main encryption password). Passwords in the Windows Credential Manager cannot be easily stolen even by malicious software on your computer, because these passwords are not given to the credential manager in plain text. Instead, they in turn are encrypted in a way that is tied to the machine. So if a password is extracted from Windows Credential Manager and added on another machine, it will not work. Even a hacker cannot easily extract plain text Syncovery passwords from Windows Credential Manager.
The detailed choices for encryption can be found on the first tab sheet of the Program Settings dialog.
The encryption algorithm used is AES-256.
Another improvement since version 9.40 is that password are also encrypted while stored in memory. If you create a memory dump with Task Manager, you will not be able to find any passwords, unless you are currently editing a profile.